
DDoS Protection
Inline, surgical mitigation for attacks against hosting, game, voice and network services.
Our approach
Hosting providers and online businesses are frequently targeted by DDoS attacks. SmartMitigate is our own mitigation solution and integrates into our existing cluster of vendor-based mitigators.
Inline mitigation
Traffic is inspected continuously. We support IPv4, IPv6, packet samples, portal access and API-based visibility.
What sets us apart
We do not treat country blocking as DDoS mitigation. We work with known countermeasures such as SYN cookies, TCP and UDP authentication, and attack patterns that clearly identify harmful traffic.
Built for real attack traffic
SmartMitigate is designed for long-lasting attacks, game and voice traffic, packet samples, rich statistics and custom mitigation profiles.
Inline
Traffic is inspected at all times.
Rich statistics
All attacks in one portal or via REST API.
Packet samples
Analyse captured packet samples on your own.
Many vectors
TCP, UDP, ICMP, GRE and IPv6.
Game and voice
TeamSpeak, FiveM, Minecraft and others.
Custom mitigation
Tailored policies for special workloads.
What we can mitigate
SMARTNET mitigates network-layer and transport-layer attacks for IPv4 and IPv6. Layer 7 HTTP(S) floods and real application bot traffic require application-side controls and are not covered by our DDoS mitigators.
Supported attack types
- IPv4 and IPv6 floods
- UDP floods
- TCP floods
- ICMP floods
- Other protocol floods
- Resource exhaustion attacks
- Amplification floods
- PCAP replay protection
- Zero-day attack detection where standard countermeasures are not enough
Not fully covered
- Layer 7 HTTP(S) floods
- Real application bot traffic such as Minecraft bots
- Application logic abuse that looks like valid user traffic
We do not provide support for Layer 7 HTTP(S) floods because those attacks must be handled at the application layer, not on the layer where SmartMitigate operates on.
Application-specific mitigation
SmartMitigate is our own anti-DDoS system for application-specific attacks. It enforces strict TCP and UDP authentication and is designed for game, voice and high-risk services.
For TCP services, SmartMitigate should be enabled permanently. If it is only enabled after an attack is detected, existing TCP clients may be disconnected when the mitigation profile changes.
Permanent protection
UDP traffic and selected TCP ranges can permanently flow through SmartMitigate before being sent back to the generic mitigation layer.
Custom mitigation profiles
Customers can request custom mitigation profiles for specific applications. If the filter benefits many customers, we may develop it for free. Complex one-off requests may require paid development.
Source whitelisting
SmartMitigate supports source whitelisting based on LPM matches. Whitelisted sources can still be limited if they become part of an attack.
Supported game and application ranges
Use the supported port ranges. Do not run games or VPN services outside their specified ranges and do not mix unrelated applications into game-specific ranges.
UDP ranges
TCP ranges
Currently active permanent SmartMitigate ranges
UDP traffic and FiveM TCP traffic on ports 30000-32000 are currently routed through SmartMitigate permanently.
Limits and blocked traffic
Traffic that may be rate limited
- TCP traffic
- UDP traffic
- DNS traffic per destination IP
Public resolvers such as 1.1.1.1, 8.8.8.8 and 9.9.9.9 receive higher priority during DNS-related attacks.
Blocked by default
- IPv4 GRE traffic unless whitelisted
- Non-IP protocol traffic except proto 1, 4, 6 and 17
GRE and other protocols are blocked by default because they cannot be mitigated safely without knowing the expected source and destination pairs. GRE tunnels can be whitelisted via SmartRules in our customer interface.
Mitigation capacity and expectations
SMARTNET includes up to 1 Tbps / 1 Gpps guaranteed mitigation capacity for each customer. Larger attacks are also mitigated where possible, but we reserve the right to blackhole or discard traffic if an attack significantly impacts the network.
Included baseline
Up to 1 Tbps / 1 Gpps mitigation capacity is included regardless of monthly recurring charge.
Above 1 Tbps / 1 Gpps
Larger attacks are not automatically blackholed. We may ask for more information about the attacked service or offer a higher-capacity plan.
Best effort
DDoS protection is provided on a best-effort basis. We do not provide an SLA for mitigation capacity or attack-related availability.
GRE tunnels are available, but not ideal for every service
GRE tunnels are an easy way to receive DDoS protection from SMARTNET. For latency-critical services such as game servers, a physical interconnect is usually the better option.
Not recommended: MikroTik GRE
Many MikroTik routers cannot handle GRE traffic above 1 Gbps. We do not provide support for MikroTik-based GRE endpoints.
Not recommended: cross-continent GRE
We do not recommend SMARTNET GRE tunnels when the customer endpoint is outside Europe. Cross-continent GRE is harder to troubleshoot and can add avoidable latency or congestion.
Anti-DDoS offers
Mitigation via GRE, cross-connect or custom setup.
GRE tunnel
- BGP or Layer-2 / static routing
- IPv6 and IPv4
- Location: Equinix FR5
- Redundant setup
- /30 IPv4 and /128 IPv6
- 1 Gbps 95/5 clean traffic included
- 24/7 support
Custom solution
- Fully managed
- Location: Equinix FR5
- Custom routing and filtering policy
- For special workloads and larger deployments
Cross-connect
- BGP or static routing
- IPv6 and IPv4
- Jumbo-frame ready
- Location: Equinix FR5
- Redundant setup
- /30 IPv4 and /128 IPv6
- Starting from 1 Gbps 95/5
- 1, 10, 25 or 40G ports
- 24/7 support
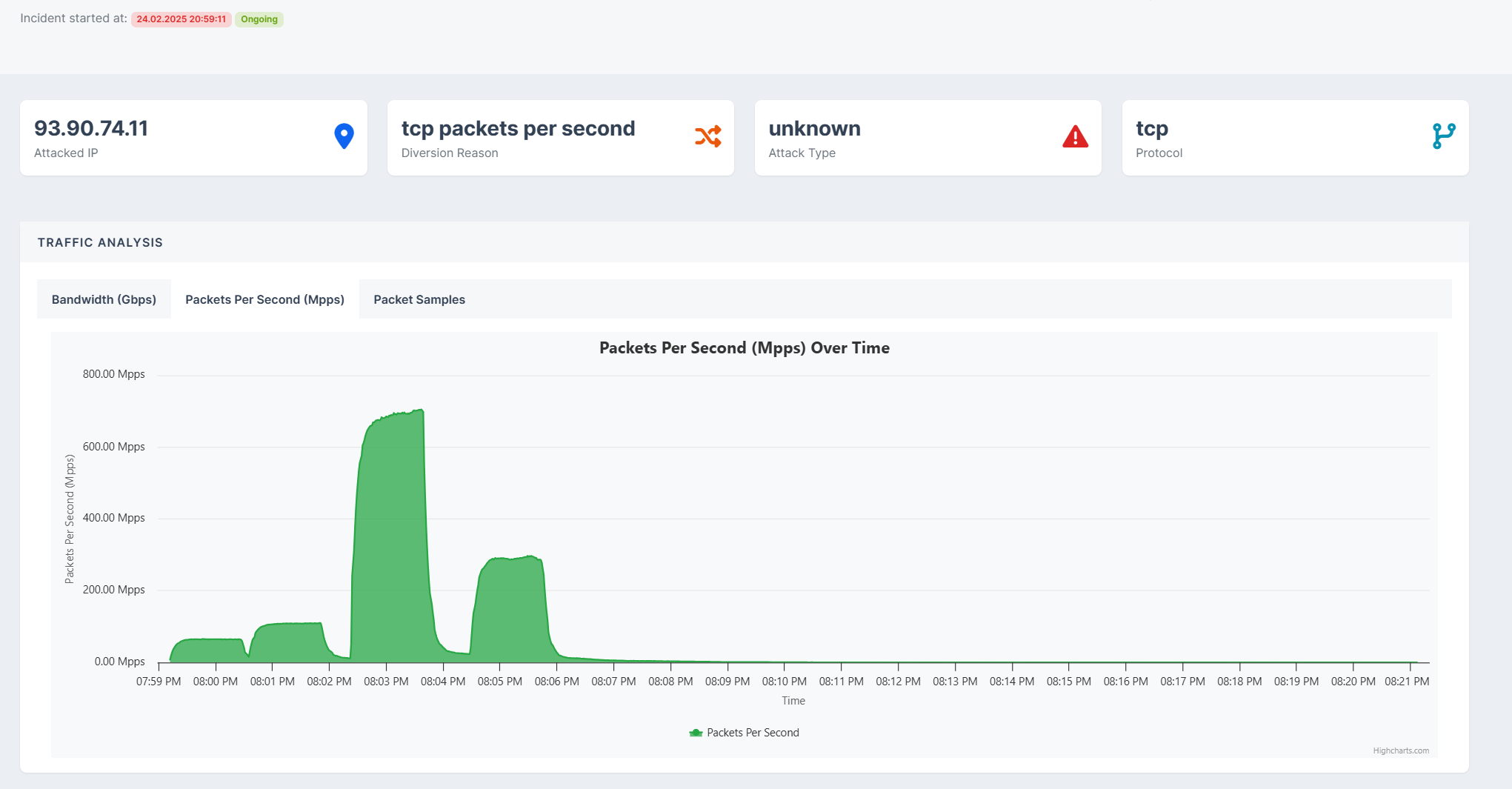
War and peacetime traffic insight
Attack overview, packet samples and filter visibility through the customer portal.
AI-assisted filters against PCAP replay and zero-day threats
Your benefits
- Time-to-mitigate under 10 seconds
- Optimised for latency-critical apps below 0.2 ms
- Cost-effective: pay for clean traffic only
- Detailed attack reporting via portal or REST API
- Mitigation via BGP / GRE or L1 / L2 transport
- Custom zones per IP
- Game server protection: Minecraft, FiveM, CS 1.6
- Voice server protection: TeamSpeak, Mumble
- Coverage for UDP, TCP, GRE and ICMP services
- Pre-filters against amplification
- Zero-day pattern detection
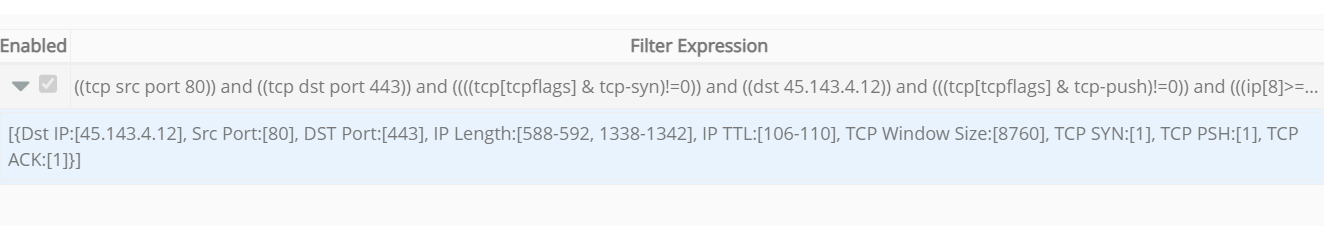
- Flexible custom BPF rules
DDoS protection FAQ
Practical details about pricing, SmartRules, supported traffic and mitigation behaviour.
Open questions or need an offer?
Contact our team to discuss your traffic profile and mitigation requirements.
